
Please Wait...
Pass4Future also provide interactive practice exam software for preparing Eccouncil Certified SOC Analyst v2 (312-39) Exam effectively. You are welcome to explore sample free Eccouncil 312-39 Exam questions below and also try Eccouncil 312-39 Exam practice test software.
Do you know that you can access more real Eccouncil 312-39 exam questions via Premium Access? ()
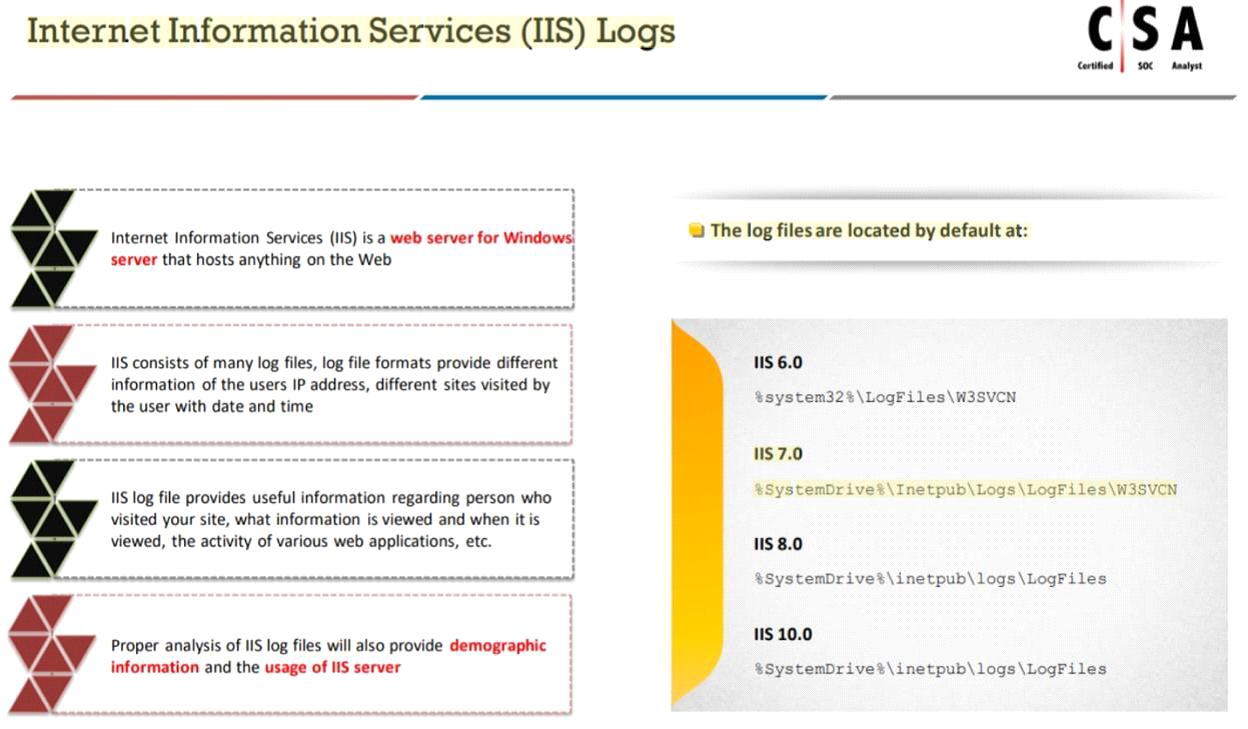
Harley is working as a SOC analyst with Powell Tech. Powell Inc. is using Internet Information Service (IIS) version 7.0 to host their website.
Where will Harley find the web server logs, if he wants to investigate them for any anomalies?
Answer : A
Which of the following is a set of standard guidelines for ongoing development, enhancement, storage, dissemination and implementation of security standards for account data protection?
Answer : C
What does the HTTP status codes 1XX represents?
Answer : A
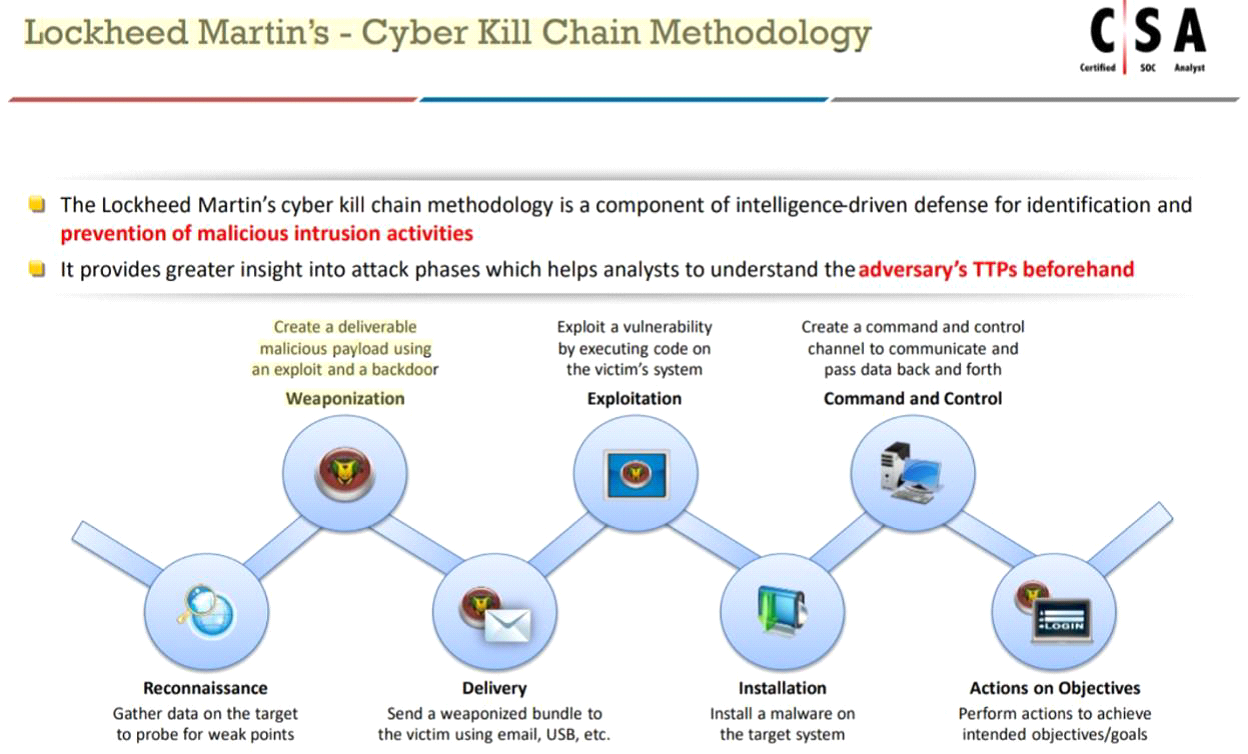
In which phase of Lockheed Martin's -- Cyber Kill Chain Methodology, adversary creates a deliverable malicious payload using an exploit and a backdoor?
Answer : C
Identify the attack, where an attacker tries to discover all the possible information about a target network before launching a further attack.
Answer : D