
Please Wait...
Pass4Future also provide interactive practice exam software for preparing Fortinet NSE 6 - FortiClient EMS 7.4 Administrator (FCP_FCT_AD-7.4) Exam effectively. You are welcome to explore sample free Fortinet FCP_FCT_AD-7.4 Exam questions below and also try Fortinet FCP_FCT_AD-7.4 Exam practice test software.
Do you know that you can access more real Fortinet FCP_FCT_AD-7.4 exam questions via Premium Access? ()
Which security fabric component sends a notification io quarantine an endpoint after IOC detection "n the automation process?
Answer : C
Understanding the Automation Process:
In the Security Fabric, automation processes can include actions such as quarantining an endpoint after an IOC (Indicator of Compromise) detection.
Evaluating Responsibilities:
FortiClient EMS plays a crucial role in endpoint management and can send notifications to quarantine endpoints.
Conclusion:
The correct security fabric component that sends a notification to quarantine an endpoint after IOC detection is FortiClient EMS.
FortiClient EMS and automation process documentation from the study guides.
Refer to the exhibit.
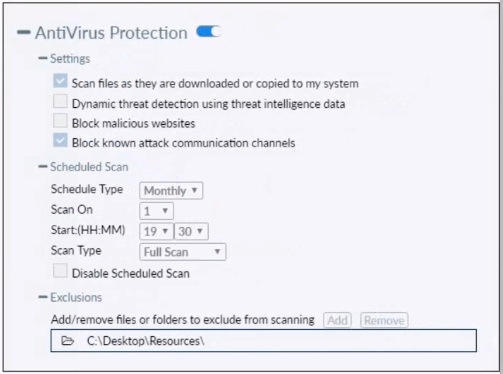
Based on the settings shown in the exhibit which statement about FortiClient behavior is true?
Answer : A
Action On Virus Discovery Warn the User If a Process Attempts to Access Infected Files Quarantine Infected Files. You can use FortiClient to view, restore, or delete the quarantined file, as well as view the virus name, submit the file to FortiGuard, and view logs. Deny Access to Infected Files Ignore Infected Files
An administrator must add an authentication server on FortiClient EMS in a different security zone that cannot allow a direct connection.
Which solution can provide secure access between FortiClient EMS and the Active Directory server?
Answer : A
Requirement:
The administrator needs to add an authentication server on FortiClient EMS in a different security zone that cannot allow a direct connection.
Solution Analysis:
The goal is to securely connect FortiClient EMS and the Active Directory server despite being in different security zones.
Evaluating Options:
Installing FortiClient EMS on the same VM as Active Directory (option B) is not practical due to security zone separation.
Configuring a slave FortiClient EMS on a virtual machine (option C) does not address the need for secure communication.
Configuring an Active Directory connector (option D) may not be sufficient without secure routing.
Conclusion:
Deploying a FortiGate device between FortiClient EMS and the Active Directory server ensures secure and controlled access between the two zones.
FortiClient EMS and FortiGate configuration and deployment documentation from the study guides.
A FortiClient EMS administrator is implementing additional security on FortiClient for compliance checks. Which tags can the administrator configure to detect endpoints based on vulnerability severity levels? (Choose one answer)
Answer : D
According to the FortiClient EMS 7.2/7.4 Administration Guide and the ZTNA Deployment Guide, the administrator can configure Security posture tags (also known as Zero Trust Network Access (ZTNA) tags in recent versions) to detect and group endpoints based on specific compliance criteria, including vulnerability severity levels.
1. How Security Posture Tags Work for Vulnerabilities:
Tagging Rules: Under the Security Posture Tags (or Zero Trust Tags) section in EMS, an administrator creates a new rule set and adds a rule.
Rule Type: The administrator selects the Vulnerable Devices rule type.
Severity Levels: Within this rule, the administrator can specify the Severity Level (such as Critical, High, Medium, or Low). EMS dynamically applies the tag to any endpoint where the vulnerability scan detects at least one vulnerability matching or exceeding that severity level.
Dynamic Grouping: These tags allow for dynamic grouping of endpoints, which can then be synchronized with a FortiGate to enforce access control based on the device's current security posture.
2. Why Other Options are Incorrect:
A . Outbreak alert tags: While FortiGuard Outbreak alerts can be used in tagging, they specifically target endpoints vulnerable to a particular 'outbreak' or high-profile threat currently active in the wild, rather than providing a general mechanism for all vulnerability severity levels.
B . Classification tags: These tags are typically used for broader endpoint identification (like department or location) and sending information to FortiAnalyzer for reporting, rather than real-time security posture compliance based on vulnerability scans.
C . Fabric tags: 'Fabric' usually refers to the integration between Fortinet devices (the Security Fabric). While tags are shared across the Fabric, the specific tags configured within EMS for endpoint detection based on posture are categorized as Security Posture/Zero Trust tags.
3. Curriculum Reference:
FortiClient EMS Administration Guide (Zero Trust Tagging Rules section): Explicitly details the 'Vulnerable Devices' rule type and its severity options.
EMS Study Guide (Compliance & Vulnerability): Describes using these tags to ensure endpoints meet minimum security standards before being granted access to the network.
An administrator needs to connect FortiClient EMS as a fabric connector to FortiGate What is the prerequisite to get FortiClient EMS lo connect to FortiGate successfully?
Answer : A
Connecting FortiClient EMS to FortiGate:
The administrator needs to establish a connection between FortiClient EMS and FortiGate as a fabric connector.
Prerequisites for Connection:
A key prerequisite is the import and verification of the FortiClient EMS tool CA certificate on FortiGate to ensure a trusted connection.
Conclusion:
The correct prerequisite for a successful connection is to import and verify the FortiClient EMS tool CA certificate on FortiGate.
FortiClient EMS and FortiGate connection and certificate management documentation from the study guides.