
Please Wait...
Pass4Future also provide interactive practice exam software for preparing Fortinet NSE 6 - OT Security 7.6 Architect (NSE6_OTS_AR-7.6) Exam effectively. You are welcome to explore sample free Fortinet NSE6_OTS_AR-7.6 Exam questions below and also try Fortinet NSE6_OTS_AR-7.6 Exam practice test software.
Do you know that you can access more real Fortinet NSE6_OTS_AR-7.6 exam questions via Premium Access? ()
Refer to the exhibit.
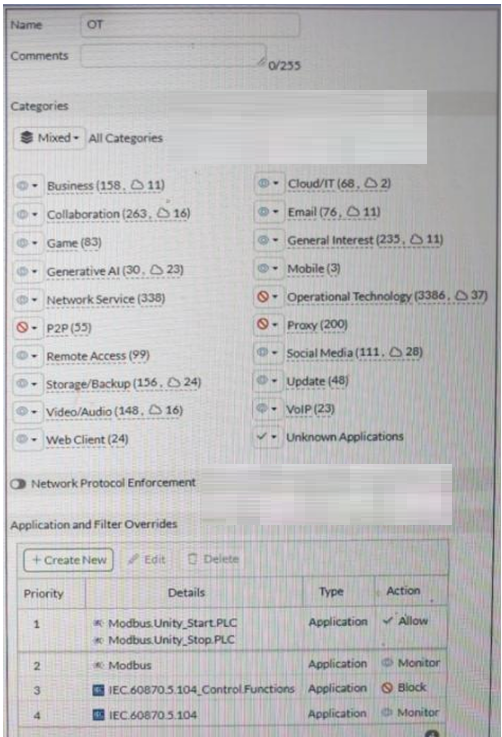
A partial Application Sensor profile is shown. When you apply this profile in a firewall policy, which two statements are correct? (Choose two answers)
Answer : A, C
The correct answers are A and C.
Option C is correct because the profile clearly contains the Operational Technology category and specific OT application signatures such as Modbus and IEC.60870.5.104. The study guide says ''You can use application control signatures to detect OT protocols'' and ''You can filter to a specific OT protocol.'' That means OT application signatures are active in this sensor profile.
Option A is correct because the guide explains that application control works at different levels: ''Detection of protocol (one detection per session)'' and ''Message level (one detection per protocol message).'' It also says you can use application signatures for ''granular message type identification.'' In the exhibit, IEC.60870.5.104.Control.Functions is explicitly configured, which is a granular IEC message/control-level signature rather than only a protocol-level match. That means logging and control can occur at the IEC command level.
Option B is not correct because the profile shows Modbus configured at the parent protocol level as Monitor, while the guide states that the ''parent signature takes precedence over the child signature.'' Since protocol-level detection is one detection per session, that does not mean FortiGate will necessarily log each Modbus command individually.
Option D is incorrect because even though the broader Operational Technology category is set to block, the profile includes specific application and filter overrides for Modbus and IEC 104 behavior. So the resulting effect is not simply that all OT protocols are blocked.
Refer to the exhibit.

A partial OT network is shown. In this OT network, you must add additional security measures to detect OT protocols and, therefore, increase the traffic visibility. Which security sensor must you implement to detect the OT protocols in this network? (Choose one answer)
Answer : C
The correct answer is C. Application sensor set to monitor on all the FortiGate devices.
The study guide clearly explains that application control is the feature used to identify OT protocols. It states that ''application control detects the protocols used in applications like Modbus, IEC 104, and the contents of the telecontrol messages'' and also says ''You can use application control signatures to detect OT protocols.'' It further shows an example where a Modbus application control profile is enabled on a firewall policy ''for OT protocol visibility in the monitor status.'' This directly matches the requirement in the question, which is to detect OT protocols and increase traffic visibility.
The other options do not fit the requirement as precisely. Device detection is for identifying devices and collecting endpoint information, not for detecting industrial protocols. Inline IDS and IPS are focused more on detecting or blocking attacks, exploits, protocol abnormalities, and known vulnerabilities. While IPS can inspect some OT traffic, the study guide distinguishes it from application control by stating that IPS signatures tend to detect exploits, whereas application control signatures tend to provide protocol detection at various levels. Therefore, the required security sensor for OT protocol detection and traffic visibility is the application sensor in monitor mode.
Refer to the exhibit.
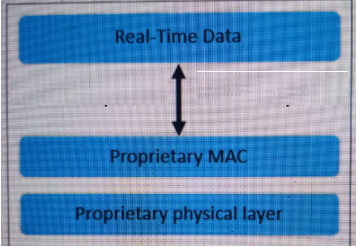
An industrial Ethernet protocol skipping layers 3 to 6 is shown. Which industrial Ethernet protocol is it? (Choose one answer)
Answer : D
The correct answer is D. EtherCAT. The study guide explicitly states under the Ethernet/IP and EtherCAT section that ''EtherCAT is a protocol that offers real-time communication in a primary-secondary configuration'' and ''EtherCAT skips layers 3 to 6 to deliver real-time communication.'' It also adds that ''the most important feature of this protocol is that secondary devices collect only the information they need from the data packets.'' This matches the exhibit exactly, where the diagram shows Real-Time Data above a Proprietary MAC and Proprietary physical layer, reflecting the protocol structure that bypasses the intermediate OSI layers.
The other options do not match this behavior. The guide says POWERLINK uses layer 2 and layer 7 of the OSI model, not that it skips layers 3 to 6. It also explains that Ethernet/IP is the industrial protocol based entirely on Ethernet standards and adapts to the OSI model. Modbus is described as an open client/server protocol and is not suitable for transmitting data in real time. Therefore, the protocol in the exhibit is clearly EtherCAT.
Refer to the exhibit.

The OT devices behind the ruggedized FortiGate have vulnerabilities and you want to apply a virtual patching profile in the firewall policy. Why is Virtual Patching not available in the Security Profiles section? (Choose one answer)
Answer : A
The correct answer is A. You must enable Virtual Patching in the Feature Visibility section.
The study guide states clearly that ''By default, virtual patching profiles are hidden on the GUI, and you must enable them through System > Feature Visibility.'' That exactly matches the situation in the exhibit, where Virtual Patching does not appear under Security Profiles. So the issue is not that the feature is unsupported, but that it is simply hidden in the GUI until it is enabled.
The other options do not answer the question being asked. A valid OT security service license is required for virtual patching signatures and protection workflow, and OT signatures are relevant to IPS-based OT protection, but those do not explain why the menu item itself is missing from the Security Profiles section. The guide specifically identifies Feature Visibility as the reason the Virtual Patching profile is not shown in the GUI. Therefore, the required action is to enable Virtual Patching in System > Feature Visibility.
In the Purdue model, at which level are physical assets like the Industrial Internet of Things (IIoT) placed? (Choose one answer)
Answer : D
According to the OT Security 7.6 Architect study guide regarding the Purdue Model:
Asset Location: The study guide states that 'All critical physical assets are located on the plant floor and equipped with IIoT sensors.'
Level Classification: The 'plant floor' is further defined as the 'control area zone,' which consists of Levels 0, 1, and 2.
Hierarchy: The 'Operations & Control' zone is identified as Level 3 and Level 3.5.
Direct Answer: In the 'Introduction' lesson's Knowledge Check, the specific question 'In