
Please Wait...
Pass4Future also provide interactive practice exam software for preparing GIAC Systems and Network Auditor (GSNA) Exam effectively. You are welcome to explore sample free GIAC GSNA Exam questions below and also try GIAC GSNA Exam practice test software.
Do you know that you can access more real GIAC GSNA exam questions via Premium Access? ()
You have made a program secure.c to display which ports are open and what types of services are running on these ports. You want to write the program's output to standard output and simultaneously copy it into a specified file. Which of the following commands will you use to accomplish the task?
Answer : D
You will use the tee command to write its content to standard output and simultaneously copy it into the specified file. The tee command is
used to split the output of a program so that it can be seen on the display and also be saved in a file. It can also be used to capture
intermediate output before the data is altered by another command or program. The tee command reads standard input, then writes its
content to standard output, and simultaneously copies it into the specified file(s) or variables. The syntax of the tee command is as follows:
tee [-a] [-i] [File]
where, the -a option appends the output to the end of File instead of writing over it and the -i option is used to ignore interrupts.
Answer A is incorrect. The concatenate (cat) command is used to display or print the contents of a file.
Syntax:
cat filename
For example, the following command will display the contents of the /var/log/dmesg file:
cat /var/log/dmesg
Note: The more command is used in conjunction with the cat command to prevent scrolling of the screen while displaying the contents of a file.
Answer C is incorrect. The less command is used to view (but not change) the contents of a text file, one screen at a time. It is similar
to the more command. However, it has the extended capability of allowing both forward and backward navigation through the file. Unlike
most Unix text editors/viewers, less does not need to read the entire file before starting; therefore, it has faster load times with large files.
The command syntax of the less command is as follows:
less [options] file_name
Where,
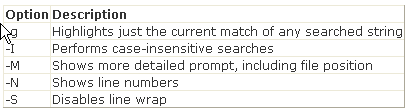
Answer B is incorrect. The more command is used to view (but not modify) the contents of a text file on the terminal screen at a time.
The syntax of the more command is as follows:
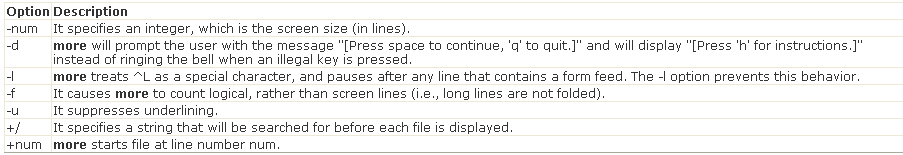
more [options] file_name
Where,
Victor wants to use Wireless Zero Configuration (WZC) to establish a wireless network connection using his computer running on Windows XP
operating system. Which of the following are the most likely threats to his computer?
Each correct answer represents a complete solution. Choose two.
Answer : A, C
Wireless Zero Configuration (WZC), also known as Wireless Auto Configuration, or WLAN AutoConfig is a wireless connection management
utility included with Microsoft Windows XP and later operating systems as a service that dynamically selects a wireless network to connect to
based on a user's preferences and various default settings. This can be used instead of, or in the absence of, a wireless network utility from
the manufacturer of a computer's wireless networking device. The drivers for the wireless adapter query the NDIS Object IDs and pass the
available network names to the service. WZC also introduce some security threats, which are as follows:
WZC will probe for networks that are already connected. This information can be viewed by anyone using a wireless analyzer and can
be used to set up fake access points to connect.
WZC attempts to connect to the wireless network with the strongest signal. Attacker can create fake wireless networks with high-
power antennas and cause computers to associate with his access point.
Answer D is incorrect. WZC does not interfere in the configuration of encryption and MAC filtering.
Answer B is incorrect. In a ping flood attack, an attacker sends a large number of ICMP packets to the target computer using the ping
command, i.e., ping -f target_IP_address. When the target computer receives these packets in large quantities, it does not respond and
hangs.
Which of the following statements about Secure Sockets Layer (SSL) are true?
Each correct answer represents a complete solution. Choose two.
Answer : C, D
Secure Sockets Layer (SSL) is a protocol used to transmit private documents via the Internet. SSL uses a combination of public key and
symmetric encryption to provide communication privacy, authentication, and message integrity. Using the SSL protocol, clients and servers can
communicate in a way that prevents eavesdropping and tampering of data on the Internet. Many Web sites use the SSL protocol to obtain
confidential user information, such as credit card numbers. By convention, URLs that require an SSL connection start with https: instead of
http:. By default, SSL uses port 443 for secured communication.
For a SSL connection between a Web browser and Web server, you must enter https, for example, 'https://www.vzen.com', instead of http
as the protocol type in the URL. This will instruct the Web browser to use a different port for communication. SSL uses TCP port 443 for
communication.
Fill in the blank with the appropriate term.
When two routers are used in a firewall configuration, the internal router is known as a .
Correct
See Below Explanation:
interior router present in the screened host firewall architecture. It is attached to the perimeter network and protects the internal network
from the Internet and the perimeter net.
A choke router is basically employed for the job of packet filtering for the firewall. It is also used to provide access to selected services that
are outbound from the internal net to the Internet. These services may include outgoing Telnet, FTP, WAIS, Archie, Gopher, etc.
Answer : A
interior router present in the screened host firewall architecture. It is attached to the perimeter network and protects the internal network
from the Internet and the perimeter net.
A choke router is basically employed for the job of packet filtering for the firewall. It is also used to provide access to selected services that
are outbound from the internal net to the Internet. These services may include outgoing Telnet, FTP, WAIS, Archie, Gopher, etc.
You work as a Network Administrator for Tech Perfect Inc. For security issues, the company requires you to harden its routers. You therefore
write the following code:
Router#config terminal
Router(config) #no ip bootp server
Router(config) #no ip name-server
Router(config) #no ntp server
Router(config) #no snmp server
Router(config) #no ip http server
Router(config) #^Z
Router#
What services will be disabled by using this configuration fragment?
Each correct answer represents a complete solution. Choose all that apply.
Answer : A, D
The above configuration fragment will disable the following services from the router:
The BootP service
The DNS function
The Network Time Protocol
The Simple Network Management Protocol
Hyper Text Transfer Protocol