
Please Wait...
Pass4Future also provide interactive practice exam software for preparing Juniper Security, Professional (JN0-636) Exam effectively. You are welcome to explore sample free Juniper JN0-636 Exam questions below and also try Juniper JN0-636 Exam practice test software.
Do you know that you can access more real Juniper JN0-636 exam questions via Premium Access? ()
Exhibit:
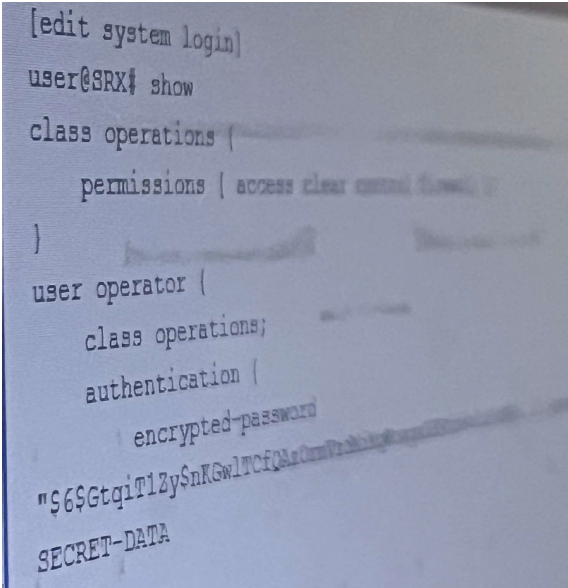
Referring to the exhibit, the operator user is unable to save configuration files to a usb stick the is
plugged into SRX. What should you do to solve this problem?
Answer : B
To solve the problem of the operator user being unable to save configuration files to a USB stick that is plugged into SRX, you need to add the system-control permission flag to the operations class. The other options are incorrect because:
Enter the configuration mode: user@host> configure
Navigate to the system login class hierarchy: user@host# edit system login class operations
Add the system-control permission flag: user@host# set permissions system-control
Commit the changes: user@host# commit
How to mount a USB drive on EX/SRX/MX/QFX Series platforms to import/export files
Exhibit:
You are troubleshooting a firewall filter shown in the exhibit that is intended to log all traffic and block
only inbound telnet traffic on interface ge-0/0/3.
How should you modify the configuration to fulfill the requirements?
Answer : A
To modify the configuration to fulfill the requirements, you need to modify the log-all term to add the next term action. The other options are incorrect because:
Enter the configuration mode: user@host> configure
Navigate to the firewall filter hierarchy: user@host# edit firewall family inet filter block-telnet
Add the next term action to the log-all term: user@host# set term log-all then next term
Commit the changes: user@host# commit
you configured a security policy permitting traffic from the trust zone to the untrust zone but your
traffic not hitting the policy.
In this scenario, which cli command allows you to troubleshoot traffic problem using the match criteria?
Answer : C
To troubleshoot the traffic problem using the match criteria, you need to use the show security match-policies CLI command. The other options are incorrect because:
In an effort to reduce client-server latency transparent mode was enabled an SRX series device.
Which two types of traffic will be permitted in this scenario? (Choose Two )
Answer : A, B
The other options are incorrect because:
ARP Support in Transparent Mode
Layer 2 Non-IP Multicast Traffic Support in Transparent Mode
Exhibit:
Referring to the exhibit, your company's infrastructure team implemented new printers
To make sure that the policy enforcer pushes the updated Ip address list to the SRX.
Which three actions are required to complete the requirement? (Choose three )
Answer : A, B, C
Referring to the exhibit, your company's infrastructure team implemented new printers. To make sure that the policy enforcer pushes the updated IP address list to the SRX, you need to perform the following actions:
The other options are incorrect because:
D) Configuring Security Director to create a C&C feed is not required to complete the requirement. A C&C feed is a security intelligence feed that contains the IP addresses of servers that are used by malware or attackers to communicate with infected hosts. The C&C feed is not related to the new printers or the dynamic address feed.
Configuring the Server Feed URL
[Command and Control Feed Overview]