
Please Wait...
Pass4Future also provide interactive practice exam software for preparing Proofpoint Certified Threat Protection Analyst (PPAN01) Exam effectively. You are welcome to explore sample free Proofpoint PPAN01 Exam questions below and also try Proofpoint PPAN01 Exam practice test software.
Do you know that you can access more real Proofpoint PPAN01 exam questions via Premium Access? ()
Based on the exhibit,
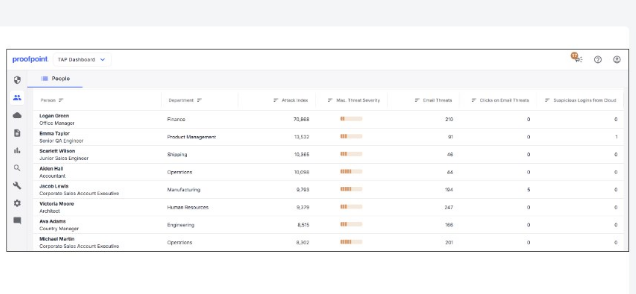
which user would most benefit from attending security awareness training based on their behavior?
Answer : D
In Proofpoint user-risk views (People page / user lists), ''behavior'' signals that drive training prioritization typically include measurable interaction with threats---especially clicks on email threats and repeated exposure patterns. The exhibit indicates that Jacob Lewis stands out behaviorally (e.g., elevated ''Clicks on Email Threats'' relative to peers and/or meaningful exposure indicators), making them the best candidate for targeted awareness intervention. From an IR preparation standpoint, training is most effective when it is risk-based and individualized: users who click are statistically more likely to become the initial foothold for credential theft and account takeover. Proofpoint programs commonly combine technical controls (URL Defense blocking, attachment detonation, post-delivery quarantine) with human controls (just-in-time coaching, targeted modules, reinforcement after real-world reports). Assigning training to high-click users reduces future incident volume by cutting successful phishing rates, improving reporting via ''Report Suspicious,'' and increasing early detection. Operationally, analysts also pair training with compensating controls for repeat clickers (stricter URL access policy, heightened monitoring, enforced MFA, mailbox rule audits) to reduce risk while behavior improves.
Which activity is part of the Preparation phase in the NIST lifecycle?
Answer : D
Preparation is the phase where organizations build readiness before incidents occur---people, process, and technology. Conducting response drill scenarios (D), such as tabletop exercises or simulation drills, is a core preparation activity because it validates playbooks, escalation paths, tooling access, and decision-making under time pressure. In Proofpoint-focused IR, drills commonly simulate credential phishing leading to account takeover, or BEC invoice fraud, requiring coordinated actions across TAP triage, Smart Search message tracing, TRAP post-delivery pulls, IAM containment (password reset/token revocation/MFA enforcement), and business verification procedures. The goal is to ensure responders can execute quickly and consistently, and to discover gaps such as missing log retention, unclear ownership for blocklists, or untested comms templates. Restoring from backups (A) is recovery, documenting postmortems (B) is post-incident activity, and identifying compromised accounts (C) is detection/analysis. In practice, preparation drills measurably reduce mean-time-to-contain by ensuring analysts already know where to find Proofpoint evidence (headers, verdicts, click telemetry) and how to trigger remediation workflows without delay.
What is a defining characteristic of Advanced Persistent Threat (APT) actors?
Answer : D
APT actors are characterized by strategic intent, persistence, and resourcing---commonly associated with state sponsorship or alignment---targeting sensitive assets such as government, defense, critical infrastructure, research IP, and executive communications. In Proofpoint-centered investigations, APT-style campaigns often show tailored lures (highly contextual pretexting), careful targeting (VIPs, finance, legal, IT), and ''low-and-slow'' operational patterns that reduce obvious malware signals. They may use credential phishing, session hijacking, or BEC-style social engineering as initial access, then pivot to living-off-the-land techniques and stealthy persistence in cloud mailboxes (inbox rules, forwarding, OAuth grants). Proofpoint telemetry (campaign clustering, threat actor mapping where available, impersonation indicators, supplier compromise signals) supports detection and scoping, but the defining attribute remains the attacker's strategic targeting and persistence rather than any single technique. This distinction matters operationally: APT suspicion raises escalation thresholds, broadens scoping (adjacent mailboxes, suppliers, cloud audit logs), increases evidence preservation rigor, and typically triggers executive/legal coordination earlier in the response lifecycle.
An attacker registers a domain like ''great-company.com'' to impersonate ''greatcompany.com.'' What tactic is being used?
Answer : C
This is a lookalike-domain tactic (C), where the attacker registers a visually similar domain to impersonate a legitimate brand. The deception relies on human pattern recognition: inserting hyphens, swapping characters, or using similar-looking TLDs so recipients perceive the domain as legitimate. In Proofpoint investigations, analysts validate lookalike domains by checking domain age (newly registered), WHOIS/registrar patterns where available, sending infrastructure (new IP ranges, mismatched rDNS), and authentication misalignment (SPF/DKIM/DMARC failures or lack of alignment). Lookalike domains are common in BEC and credential phishing: they enable ''near-perfect'' spoofing without compromising the real domain. This differs from domain hijacking (compromising a legitimate domain), display-name spoofing (only the visible name is faked), and subdomain takeover (taking control of an orphaned DNS record). For response, analysts often add the lookalike domain to blocklists, tune impostor detection policies, alert targeted recipients, and strengthen DMARC enforcement and brand monitoring to reduce future impersonation success.
What does a notification of ''Cleared'' mean when shown in the header of an individual threat tab?
Answer : B
In Proofpoint TAP/Threat Protection Workbench-style workflows, ''Cleared'' indicates the threat is no longer considered active or dangerous in the environment. This status is used after Proofpoint systems (and/or analyst actions) determine that the malicious component is neutralized---commonly because URLs are now blocked, the threat has been remediated post-delivery (pulled/quarantined), or further analysis reclassified the item as safe. In containment terms, ''Cleared'' communicates that the immediate risk has been reduced: users should not be able to access the malicious URL through URL Defense, and attachment-based threats may have been condemned and/or removed from mailboxes where applicable. IR teams still use the cleared state as a pivot point: they confirm whether any users were already impacted (clicks/credential entry), validate that remediation actions succeeded across all intended mailboxes (no ''unavailable'' gaps), and ensure preventive controls are in place (custom blocklists, authentication enforcement, banner rules, supplier controls). ''Cleared'' is not the same as ''not important''; it means the threat no longer poses an ongoing hazard, but scoping and user follow-up may still be required.