
Please Wait...
Pass4Future also provide interactive practice exam software for preparing Splunk Enterprise Certified Admin (SPLK-1003) Exam effectively. You are welcome to explore sample free Splunk SPLK-1003 Exam questions below and also try Splunk SPLK-1003 Exam practice test software.
Do you know that you can access more real Splunk SPLK-1003 exam questions via Premium Access? ()
A user recently installed an application to index NCINX access logs. After configuring the application, they realize that no data is being ingested. Which configuration file do they need to edit to ingest the access logs to ensure it remains unaffected after upgrade?
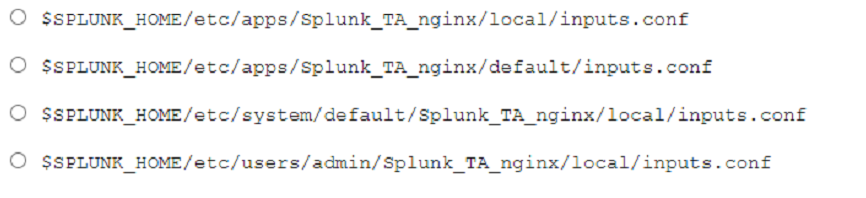
Answer : A
This option corresponds to the file path ''$SPLUNK_HOME/etc/apps/splunk_TA_nginx/local/inputs.conf''. This is the configuration file that the user needs to edit to ingest the NGINX access logs to ensure it remains unaffected after upgrade. This is explained in the Splunk documentation, which states:
The local directory is where you place your customized configuration files. The local directory is empty when you install Splunk Enterprise. You create it when you need to override or add to the default settings in a configuration file. The local directory is never overwritten during an upgrade.
What event-processing pipelines are used to process data for indexing? (select all that apply)
Answer : B, C
The indexing pipeline and the parsing pipeline are the two pipelines that are responsible for transforming the raw data into events and preparing them for indexing. The indexing pipeline applies index-time settings, such as timestamp extraction, line breaking, host extraction, and source type recognition. The parsing pipeline applies parsing settings, such as field extraction, event segmentation, and event annotation.
When using a directory monitor input, specific source types can be selectively overridden using which configuration file?
Answer : D
When using a directory monitor input, specific source types can be selectively overridden using the props.conf file.According to the Splunk documentation1, ''You can specify a source type for data based on its input and source. Specify source type for an input. You can assign the source type for data coming from a specific input, such as /var/log/. If you use Splunk Cloud Platform, use Splunk Web to define source types. If you use Splunk Enterprise, define source types in Splunk Web or by editing the inputs.conf configuration file.'' However, this method is not very granular and assigns the same source type to all data from an input.To override the source type on a per-event basis, you need to use the props.conf file and the transforms.conf file2.The props.conf file contains settings that determine how the Splunk platform processes incoming data, such as how to segment events, extract fields, and assign source types2.The transforms.conf file contains settings that modify or filter event data during indexing or search time2.You can use these files to create rules that match specific patterns in the event data and assign different source types accordingly2.For example, you can create a rule that assigns a source type of apache_error to any event that contains the word ''error'' in the first line2.
A configuration file in a deployed app needs to be directly edited. Which steps would ensure a successful deployment to clients?
Answer : C
According to the Splunk documentation1, to customize a configuration file, you need to create a new file with the same name in a local or app directory. Then, add the specific settings that you want to customize to the local configuration file. Never change or copy the configuration files in the default directory. The files in the default directory must remain intact and in their original location. The Splunk Enterprise upgrade process overwrites the default directory.
To deploy configuration files to deployment clients, you need to use the deployment server.The deployment server is a Splunk Enterprise instance that distributes content and updates to deployment clients2.The deployment server uses a directory called $SPLUNK_HOME/etc/deployment-apps to store the apps and configuration files that it deploys to clients2.To update the configuration files in this directory, you need to edit them manually and then run the command $SPLUNK_HOME/bin/sp1unk reload deploy---server to make the changes take effect2.
Therefore, option A is incorrect because it does not include the reload command. Option B is incorrect because it makes the change on a deployment client instead of the deployment server. Option D is incorrect because it changes the default directory instead of the local directory.
What event-processing pipelines are used to process data for indexing? (select all that apply)
Answer : B, D