
Please Wait...
Pass4Future also provide interactive practice exam software for preparing Splunk Cloud Certified Admin (SPLK-1005) Exam effectively. You are welcome to explore sample free Splunk SPLK-1005 Exam questions below and also try Splunk SPLK-1005 Exam practice test software.
Do you know that you can access more real Splunk SPLK-1005 exam questions via Premium Access? ()
In what scenarios would transforms.conf be used?
Answer : B
transforms.conf is used for various advanced data processing tasks in Splunk, including:
Per-Event Sourcetype: Dynamically assigning a sourcetype based on event content.
Per-Event Host Name: Dynamically setting the host field based on event content.
Per-Event Index Routing: Directing specific events to different indexes based on their content.
Option B correctly identifies these common uses of transforms.conf.
Splunk Documentation Reference: transforms.conf - Configuration
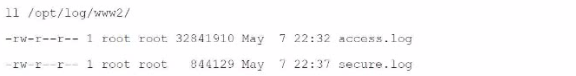
Which monitor statement will retrieve only files that start with "access" in the directory /opt/log/ww2/?
Answer : B
The correct monitor statement to retrieve only files that start with 'access' in the directory /opt/log/www2/ is [monitor:///opt/log/www2/access*]. This configuration specifically targets files that begin with the name 'access' and will match any such files within that directory, such as 'access.log'.
Splunk Documentation Reference: Monitor files and directories
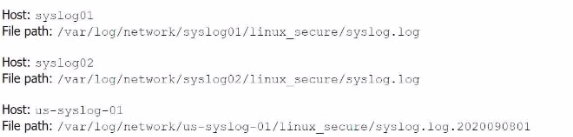
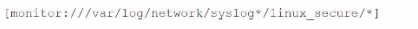
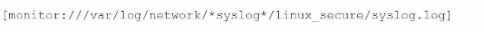
Li was asked to create a Splunk configuration to monitor syslog files stored on Linux servers at their organization. This configuration will be pushed out to multiple systems via a Splunk app using the on-prem deployment server.
The system administrators have provided Li with a directory listing for the logging locations on three syslog hosts, which are representative of the file structure for all systems collecting this dat
a. An example from each system is shown below:
A)
B)
C)

D)
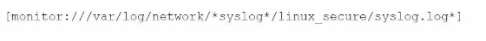
Answer : A
The correct monitor statement that will capture all variations of the syslog file paths across different systems is [monitor:///var/log/network/syslog*/linux_secure/*].
This configuration works because:
syslog* matches directories that start with 'syslog' (like syslog01, syslog02, etc.).
The wildcard * after linux_secure/ will capture all files within that directory, including different filenames like syslog.log and syslog.log.2020090801.
This setup will ensure that all the necessary files from the different syslog hosts are monitored.
Splunk Documentation Reference: Monitor files and directories
By default, which of the following capabilities are granted to the sc_admin role?
Answer : C
By default, the sc_admin role in Splunk Cloud is granted several important capabilities, including:
indexes_edit: The ability to create, edit, and manage indexes.
fsh_manage: Manage full-stack monitoring integrations.
admin_all_objects: Full administrative control over all objects in Splunk.
can_delete: The ability to delete events using the delete command.
Option C correctly lists these default capabilities for the sc_admin role.
Splunk Documentation Reference: User roles and capabilities
When creating a new index, which of the following is true about archiving expired events?
Answer : D
In Splunk Cloud, expired events can be archived to customer-managed storage solutions, such as on-premises storage. This allows organizations to retain data beyond the standard retention period if needed. [Reference: Splunk Docs on data archiving in Splunk Cloud]